Cisco Crack Password 5
James, type 5 passwords are really hard to crack, especially since Cisco uses I think the 'salted' version of the hash. That said, if you are willing to dive into some dark hacker cracker stuff, here are two links to scripts you can use (I hope posting those links does not earn me jail time). Cracking a Cisco Password. Here is a guide on how to crack a Cisco password. In this guide you will learn how to crack a Cisco hash password. Brief overview about Cisco passwords. In a Cisco equipment, there are two passwords, namely the “enable” and “telnet”. Within the Cisco “enable” command there are two ways which you can store.
- The enable password command uses the weaker type 7 encryption, whereas the enable secret command uses the stronger type 5 encryption. Cisco also has the service password-encryption command.
- Cisco’s solution to the enable password’s inherent problem was to create a new type of password called the secret password. When you configure both an enable and a secret password, the secret password is the password that will be used to switch from User Exec mode to Priv Exec mode. The following code sets both passwords for your router.
In this tutorial we will show you how to create a list of MD5 password hashes and crack them using hashcat.
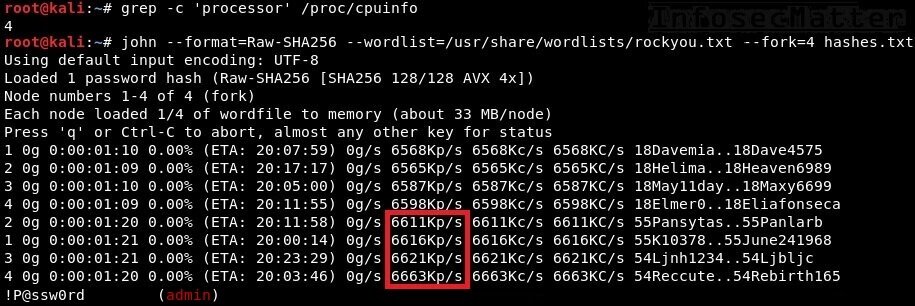
We will perform a dictionary attack using the rockyou wordlist on a Kali Linux box.
Creating a list of MD5 hashes to crack
To create a list of MD5 hashes, we can use of md5sum command.
The full command we want to use is:
Here we are piping a password to md5sum so a hash is produced. Unnecessary output is then stripped and it is stored in a file in a file called 'hashes'.
'echo -n 'Password1' is used to print the phrase 'Password1'. The -n portion removes the new line added to the end of 'Password1'. This is important as we don't want the new line characters to be hashed with our password.
The part “tr –d ‘ -‘ “ removes any characters that are a space or hyphen from the output like so:
Cisco Type 4 Password Decrypt
Before:
After:
For demonstration purposes, we'll create multiple MD5 hashes containing different strength passwords and output them to a file called hashes:
Once you have run these commands will look something like this:
If you already have a list of words then the following bash script can be used to automate the MD5 generation, reading each line in a file, then generating a file off the resulting hashes. Replace 'wordlist' with the file path of your word list.
If you do not have md5sum on your machine, you can copy and paste the hashes above and save it in a file called 'hashes'. If you want to hash different passwords than the ones above and you don't have md5sum installed, you can use MD5 generators online such as this one by Sunny Walker.
Running hashcat to Crack MD5 Hashes
Now we can start using hashcat with the rockyou wordlist to crack the MD5 hashes. The rockyou wordlist comes pre-installed with Kali. If you are not using Kali you can use another wordlist, or download it from here.
The command to start our dictionary attack on the hashes is:
| Argument | Function |
| -m 0 | Tells hashcat which mode to use. 0 is MD5. |
| Hashes | Our file containing the our MD5 password hashes. |
| /usr/share/wordlists/rockyou.txt | Points hashcat to the wordlist containing the passwords to hash and compare. |
When you run the command, you should get an output like below:
/free-download-visio-electrical-pro.html. Towards the top of the output you can see the hashes that were cracked side-by-side with the plaintext password and hash.
From the output we can determine the following passwords we hashed were not in the rockyou wordlist:
- GuessMe3
- S3CuReP455Word
- HighlyUnlik3lyToB3Cr4ck3d
Unless told otherwise, any hash that hashcat cracks will be stored in a hashcat.pot file. This will be created in directory where you ran hashcat.
The contents of your 'hashcat.pot' file from this tutorial should look like the following: https://cleaninghigh-power878.weebly.com/blog/akvis-retoucher-license-crack.
Crack Cisco Password 5 Kali
Summary
Brute Forcing Passwords Tool
This has been a basic tutorial on how to crack MD5 hashes using hashcat. We've MD5 hashed passwords and using hashcat, cracked five out of the total eight. The attack technique that we used within hashcat was a dictionary attack with the rockyou wordlist.